All business premises require security against unauthorized access. The external perimeter prevents the majority of threats prior to the reach to buildings. This guide describes the functionality of perimeter security systems in ensuring the security of assets. Knowing these systems can assist the business owners with improved security decisions.
Learning how perimeter security systems functions
What a perimeter security system includes
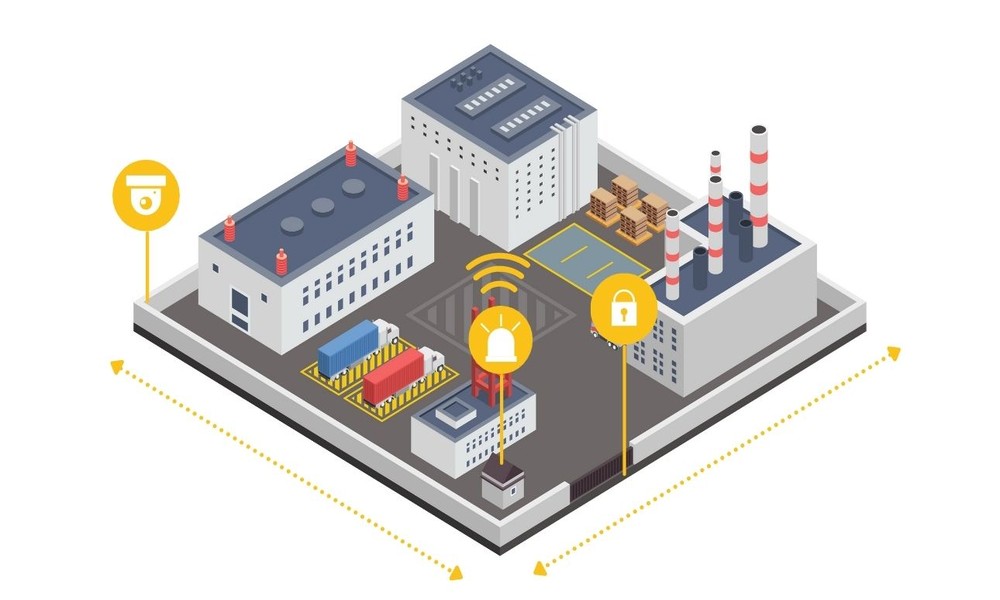
A perimeter security system is a system that integrates physical controls with electronics. The first obvious line of defense is fences, walls and gates. Electronic sensing is provided with buried cables, infrared beams and motion detectors. The entire system is completed by cameras, lights and alarms. Each of the components collaboratively detects, delays and discourages attackers.
The basic principle of how perimeter security systems work
All systems have a plain three step procedure: detect, delay and respond. The sensors identify an intruder when a boundary is crossed. Physical obstacles such as fences slow down the intruder. Cameras and alarms bring about a reaction by guards or the police. The functionality of perimeter security systems is based on this detect-delay-respond cycle.
Core components of a perimeter security system
A total perimeter defense employs a number of various technologies in an integrated manner. Any effective perimeter defense is made up of the following components.
- Physical barriers like fences and walls: The tall fence with anti-climb properties forms the initial barrier and the intruders will have to invest time and energy in crossing the barrier.
- Electronic detection sensors along the boundary: Footstep vibrations are detected by buried cables, and the movement is detected by infrared rays when an individual crosses the unseen barrier.
- Video surveillance cameras at key points: Video surveillance cameras capture all attempts of intrusion and they give visual testimony to the police or prosecution in the event of an incident.
- Motion-activated lighting systems: When sensors are activated, bright lights come on, and when intruders are surprised by sudden light, revealing their position.
- Alarm and notification devices: Sirens are loud in order to scare away intruders, and silent alerts inform security guards or monitoring centers in real-time.
How detection sensors work on a perimeter
The sensors of different types have different approaches to detect illegal entry. The most popular detection technologies can be found in the list below.
- Buried cable sensors: These cables are used to detect vibration and pressure caused by the passing of footsteps within the open field, and would be ideal in areas that are open and have no fences.
- Infrared beam sensors: The sensors have an invisible beam that they emit through a passage, and once the beam is broken an alarm is emitted.
- Microwave sensors: These devices are those that emit waves which reflect off moving objects and a variation on the pattern of the returning waves triggers an alert.
- Fence mounted vibration sensors: These are directly attached to the fabric of the fence and they sense any vibrations, or attempts to cut, or climb the fence.
- Passive infrared motion detectors: This detects body heat passing over an area, and is effective in a small area such as the gatehouses, or building edges.
How physical barriers delay intruders
There will be criminals who will not be prevented by barriers, but they introduce critical delays. The barriers are slowed down by different ways as explained below.
- Anti-climb fences: These are fences with narrow mesh and no footholds and thus, it takes several minutes of effort to climb them.
- Chain link fences: These have to be cut with bolt cutters or climbing gear and cutting is very loud and attracts attention.
- Razor wire or concertina coils: These inflict harm on anyone who tries to climb over it, and the majority of intruders would not touch it at all.
- Vehicle barriers and bollards: These prevent vehicles crashing through gates, and slow down vehicle-based attacks by a long time.
- Multiple fence layers: The second fence behind the first one doubles the delay of the first layer and it seals intruders between two fences.
Conclusion
The functioning of the perimeter security systems is based on a basic detect-delay-respond system. There are physical obstacles to prevent easy access and sensors track any activity. Application of various technologies provides the greatest protection. An effective system ensures the security of business premises 24 hours on.
